Popular x64 Tags
- encryption software x64 download
- privacy x64 download
- blowfish x64 download
- twofish x64 download
- encrypt x64 download
- lock x64 download
- folder x64 download
- decryption x64 download
- decrypt x64 download
- software x64 download
- file encryption x64 download
- data security x64 download
- security x64 download
- aes x64 download
- rijndael x64 download
- protection x64 download
- password x64 download
- protect x64 download
- encryption x64 download
- encrypt file x64 download
- drive x64 download
- pdf x64 download
- disk x64 download
- data encryption x64 download
- hide x64 download
- file x64 download
- disk encryption x64 download
- des x64 download
- free x64 download
- secure x64 download
You are here: X-64-bit Download
\ Security & Privacy
\ Encryption Tools \ BestCrypt Volume Encryption
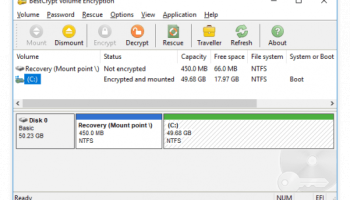
BestCrypt Volume Encryption 5.14.0
Sponsored links:
license: Demo
downloads: 370
size: 78.80 MB
updated: 2025-10-07
tags: BestCrypt Volume Encryption, download BestCrypt Volume Encryption, BestCrypt Volume Encryption free download, volume encryptor, encrypt volume, HDD encryption, encrypt, encryptor, HDD, disk
Add to Basket
Jetico, Inc.
**BestCrypt Volume Encryption by Jetico, Inc. - A Comprehensive Review**
In an era where data breaches and cyber threats are ever-increasing, securing sensitive information has become paramount. BestCrypt Volume Encryption, developed by Jetico, Inc., emerges as a robust solution designed to safeguard data through advanced encryption techniques. This software stands out for its comprehensive features, user-friendly interface, and high level of security, making it an excellent choice for both individual users and enterprises.
**Key Features**
1. **Full-Disk Encryption**: BestCrypt Volume Encryption offers full-disk encryption, ensuring that all data stored on your hard drives is protected. This includes system files, user data, and even temporary files, leaving no room for vulnerabilities.
2. **Pre-Boot Authentication**: One of the standout features is its pre-boot authentication mechanism. This ensures that unauthorized users cannot access the encrypted data without the correct credentials, providing an additional layer of security before the operating system even loads.
3. **Multiple Encryption Algorithms**: The software supports a variety of strong encryption algorithms, including AES, Serpent, and Twofish. This flexibility allows users to choose the level of security that best fits their needs.
4. **Compatibility**: BestCrypt Volume Encryption is compatible with a wide range of operating systems, including Windows, macOS, and Linux. This cross-platform support makes it a versatile tool for diverse IT environments.
5. **Ease of Use**: Despite its advanced features, the software is designed with user-friendliness in mind. The intuitive interface guides users through the encryption process, making it accessible even for those who may not be tech-savvy.
6. **Performance**: Encryption can often lead to performance degradation, but BestCrypt Volume Encryption is optimized to minimize impact on system performance. Users can continue their tasks with minimal disruption while their data remains secure.
7. **Central Management**: For enterprise users, the software offers central management capabilities. Administrators can manage encryption policies, deploy updates, and monitor compliance across multiple devices from a single console.
**Security and Compliance**
Jetico, Inc. has a strong reputation for developing security solutions, and BestCrypt Volume Encryption is no exception. The software adheres to industry standards and best practices, ensuring compliance with regulations such as GDPR and HIPAA. This makes it a reliable choice for organizations that handle sensitive data and need to meet stringent regulatory requirements.
**Support and Documentation**
Jetico provides comprehensive support and documentation for BestCrypt Volume Encryption. Users have access to detailed guides, FAQs, and a responsive support team to assist with any issues or questions that may arise. This commitment to customer support enhances the overall user experience and ensures that users can maximize the software's potential.
**Conclusion**
BestCrypt Volume Encryption by Jetico, Inc. is a powerful and reliable encryption solution that offers a high level of security for data protection. Its combination of full-disk encryption, pre-boot authentication, multiple encryption algorithms, and ease of use makes it a standout choice in the market. Whether you are an individual looking to protect personal data or an enterprise needing to secure sensitive information across multiple devices, BestCrypt Volume Encryption provides the tools and features necessary to achieve peace of mind in an increasingly digital world.
In an era where data breaches and cyber threats are ever-increasing, securing sensitive information has become paramount. BestCrypt Volume Encryption, developed by Jetico, Inc., emerges as a robust solution designed to safeguard data through advanced encryption techniques. This software stands out for its comprehensive features, user-friendly interface, and high level of security, making it an excellent choice for both individual users and enterprises.
**Key Features**
1. **Full-Disk Encryption**: BestCrypt Volume Encryption offers full-disk encryption, ensuring that all data stored on your hard drives is protected. This includes system files, user data, and even temporary files, leaving no room for vulnerabilities.
2. **Pre-Boot Authentication**: One of the standout features is its pre-boot authentication mechanism. This ensures that unauthorized users cannot access the encrypted data without the correct credentials, providing an additional layer of security before the operating system even loads.
3. **Multiple Encryption Algorithms**: The software supports a variety of strong encryption algorithms, including AES, Serpent, and Twofish. This flexibility allows users to choose the level of security that best fits their needs.
4. **Compatibility**: BestCrypt Volume Encryption is compatible with a wide range of operating systems, including Windows, macOS, and Linux. This cross-platform support makes it a versatile tool for diverse IT environments.
5. **Ease of Use**: Despite its advanced features, the software is designed with user-friendliness in mind. The intuitive interface guides users through the encryption process, making it accessible even for those who may not be tech-savvy.
6. **Performance**: Encryption can often lead to performance degradation, but BestCrypt Volume Encryption is optimized to minimize impact on system performance. Users can continue their tasks with minimal disruption while their data remains secure.
7. **Central Management**: For enterprise users, the software offers central management capabilities. Administrators can manage encryption policies, deploy updates, and monitor compliance across multiple devices from a single console.
**Security and Compliance**
Jetico, Inc. has a strong reputation for developing security solutions, and BestCrypt Volume Encryption is no exception. The software adheres to industry standards and best practices, ensuring compliance with regulations such as GDPR and HIPAA. This makes it a reliable choice for organizations that handle sensitive data and need to meet stringent regulatory requirements.
**Support and Documentation**
Jetico provides comprehensive support and documentation for BestCrypt Volume Encryption. Users have access to detailed guides, FAQs, and a responsive support team to assist with any issues or questions that may arise. This commitment to customer support enhances the overall user experience and ensures that users can maximize the software's potential.
**Conclusion**
BestCrypt Volume Encryption by Jetico, Inc. is a powerful and reliable encryption solution that offers a high level of security for data protection. Its combination of full-disk encryption, pre-boot authentication, multiple encryption algorithms, and ease of use makes it a standout choice in the market. Whether you are an individual looking to protect personal data or an enterprise needing to secure sensitive information across multiple devices, BestCrypt Volume Encryption provides the tools and features necessary to achieve peace of mind in an increasingly digital world.
OS: Windows 11, Windows Server 2019, Windows Server 2016, Windows 10 32/64 bit, Windows Server 2012 R2, Windows Server 2012, Windows 2008 R2, Windows 2008 32/64 bit, Windows 2003, Windows 8 32/64 bit, Windows 7 32/64 bit, Windows Vista, Windows XP 3
Add Your Review or 64-bit Compatibility Report
Top Encryption Tools 64-bit downloads
OpenVPN 2.7.0-I017
OpenVPN: Secure, flexible, and open-source VPN solution for privacy and remote access.
Trialware | $7.00
PenProtect 1.45
The encryption solution to secure your USB Flash Drive with AES 256 and Password
Demo | $19.00
tags: flash drive, USB, password, flash memory, pen drive, crypt, encrypt, decrypt, software, key, file, folder, AES, AES 256, security, cryptography, secure, stick, device, lock, guard flash drive, guard pen drive, penprotect
NordVPN 7.56.2.0
Secure your online privacy with NordVPN's fast, reliable VPN service.
Demo | $12.99
GhostVolt 1.3.3.0
GhostVolt: powerful data encryption, privacy, and security tool built for teams
Demo | $40.00
Twingate 2026.7.2078
Zero Trust Network Access solution for secure remote access and management.
Trialware | $5.00
Members area
Top 64-bit Downloads
-
OpenVPN x64 2.6.11
x64 open source download -
Microsoft Standalone
System Sweeper (x64 bit) 1.0.856.0 Beta
x64 freeware download -
Trend Micro Internet
Security Pro 2010 (x64
bit)
x64 trialware download -
O&O SafeErase Server
x64 18.4.611
x64 trialware download -
ThinkVantage Password
Manager 64-bit 4.0
x64 freeware download -
VSCryptoHash 64-bit 2.5.3.509
x64 freeware download -
Romaco Timeout x64 3.1.4.0
x64 freeware download -
The Enigma Protector x64 7.90
x64 demo download -
Spamihilator Portable
(x64 bit) 1.6.0
x64 freeware download -
COMODO Internet Security
(64 bit) 12.3.4.8032
x64 freeware download
Top Downloads
-
Aiseesoft Android
Unlocker 1.1.8
shareware download -
OpenVPN x64 2.6.11
open source download -
Portable SafeInCloud 24.14.1
freeware download -
OSV-Scanner 2.3.3
open source download -
abylon KEYSAFE 23.60.1
shareware download -
Twitter Password Dump 7.0
freeware download -
2FAGuard 1.7.2
open source download -
Malwarebytes Windows
Firewall Control 6.29.0.0
freeware download -
ClamWin Portable 0.103.2.1
open source download -
WebPost Tools 1.0.0.412
freeware download -
Mime Tool 2.2.8.11
freeware download -
OpenVPN 2.7.0-I017
trialware download -
CmosPwd 5.0
freeware download -
Microsoft Standalone
System Sweeper (x64 bit) 1.0.856.0 Beta
freeware download -
Kaspersky Virus Removal
Tool 20.0.14.0 (12.03.202
freeware download